The striking trend of data breaches is the biggest privacy and security concern these days. Millions of user accounts are getting leaked when large companies face hacker attacks. Yahoo hack is the biggest data breach of all. It impacted over 3 billion user accounts. Personal information ends up being sold on underground forums at miserably low prices.
SEE ALSO: How to Choose Safe YouTube Converter?
Businesses strive to comply with the latest infosec standards, however many of them do not succeed. Although the cybersecurity arena is not new, all our procedures and policies are still ineffective. In addition, companies and governments collect plenty of our private data and wish even more of it at the same time lacking appropriate initiatives to keep it safe.
Harsh laws may possibly address the problem. Collecting and storing highly sensitive information should be permitted only to those qualified and complying with the strictest standards. Additional security measures are not convenient for customers and expensive to service providers but raising the bar, in this case, is the only right solution.
We collected the best practices individuals and companies should adapt in order to keep their data safe.
15 security tips for home users
Try to observe these simple rules while browsing the Web from your home PC.
Tip 1. Do not use only one email account for everything. Create a separate email address for important stuff like banking. Nobody should know about this email account but you. Communicate with relatives, family, and friends via another email. Finally, create the 3rd account for less important things like coupon or discounts sites, dating, online games, etc.
Tip 2. Watch media privacy of your family. One of the biggest problems these days is oversharing. In particular, children and young adults are prone to publishing a great deal of sensitive data online. We should teach children what can and what cannot be disclosed on social media. Parents and schools should develop privacy and security skills in their children. Social media account’s privacy settings should be set to maximum security level possible. Sometimes it makes sense indicating the incorrect date of birth and address.
Tip 3. Be careful with files and links. Most often viruses penetrate the computer when users click on rogue links on social media, open malicious email attachments, download free stuff on torrents, or visit infected sites. Be discreet and watch your steps doing all this. 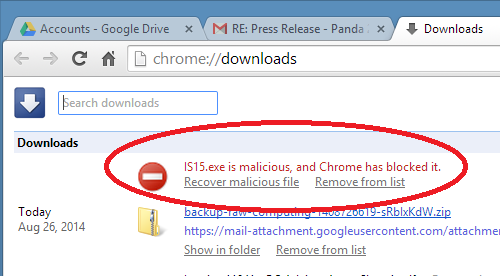
Tip 4. Install an antivirus. There are many cases when antivirus solutions fail to detect an intrusion and miss viruses. But still, having an antivirus is a must these days. Attack vectors are enormous and even the strongest security habits cannot protect from all threats. Antivirus may help in 90% of situations. Do not think it is better to have several antivirus tools. No, it is worse as they will interfere with each other’s work. However, you can employ additional antimalware on-demand scanners. Do not forget to update your security software tools as well as your OS and other software.
Tip 5. Use caution when connecting to public Wi-Fi, it can be unsafe. It is OK to do some web search or to read news while on public Wi-Fi. However, do not send important info or transfer money. Your whole communication can be put at risk. When you have to connect to public Wi-Fi try to always use VPN services. VPN hides your real IP and encrypts your traffic. Your home wireless network should be protected too. Use long passwords and whitelist (allow) only your own and family devices to connect to it.
SEE ALSO: How to Download YouTube Videos with a Proxy Server
Tip 6. The consequent advice that is old as hills is to employ strong passwords. It is ideal to use passphrases. Create separate passphrases for each new website or app. When possible enable the multi-factor authentication.
SEE ALSO: Best 3 Password Managers to Secure Personal Data
Tip 7. Use separate credit cards for online shopping as cards are crooks’ best-loved targets. Ask your bank to implement additional protection code and withdrawal limits.
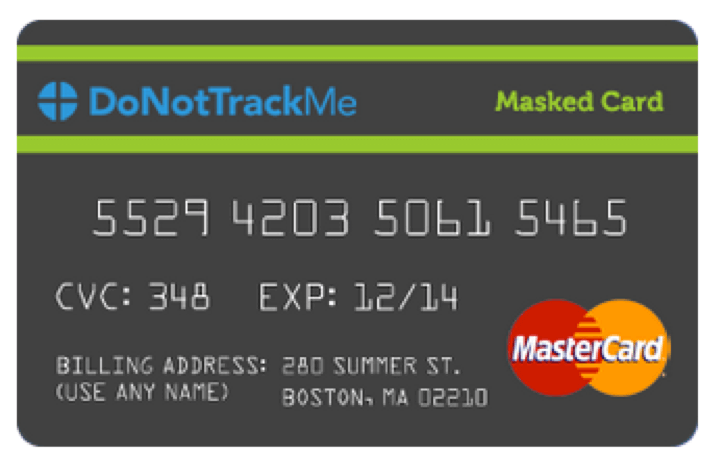
Tip 8. To spot unauthorized transactions, check each credit and debit card transaction statements on weekly basis, desirably even more often. If you notice a transaction you didn’t made, contact your bank immediately to block the card.
Tip 9. Back up, back up, back up! Ransomware is the prevalent threat these days. It may encrypt and destroy all files. It may also steal data. Use multiple backup strategies. Consider both offline and cloud storages.
SEE ALSO: How to Back up Movies Collection with DVD Ripper Software
Tip 10. Watch your contacts. Messages from relatives and friends may be dicey as thousands upon thousands of social media, messaging apps, and email accounts are getting hacked on daily basis. Crooks may hack your friend and send you a virus on his behalf. When you are unsure about a ZIP archive or strange link, it is better to verify with the sender over the phone if he sent it.
Tip 11. A rule of thumb for online shoppers is checking if the site uses HTTPS and the certificate is valid.
Tip 12. Install ad blockers on all your web browsers. If some ads still preserve and look suspicious – do not click on them. Scam masters use wise tricks, if something looks too good to be true it is better to stay away.
Tip 13. Don’t share your personal info without the need. You should not instantly and without thinking provide your social security number or other personal information to everyone who requests it.
Tip 14. Check all your gadgets’ settings for data they may transfer into the cloud. Switch off all the options you find suspicious.
Tip 15. Signing up for any services, always check their reviews. Entrust your private data only to those that have the solid protection of customer info. Previous data breaches should be a red flag.
10 security tips for businesses
Security rules for companies are stricter. Forward this list to your boss if none of them is observed at your workplace.
Tip 1. Security informing. Staff members always represent a chink in any company’s cyber armor. Employees require constant security training. Spear-phishing and safe browsing drills are a must. Implementing profound employee hiring and dismissal procedures are also very important.
Tip 2. Safe vendors choice. Quite a few breaches are accomplished through hacking smaller firms that are vendors or partners of bigger enterprises. Those small third-party subcontractors usually have lower protection capabilities and are easy targets. Businesses should choose their vendors wisely and stick only with those who employ the best security practices and standards.
Tip 3. Physical security of equipment and offices is very important even for purely online businesses. A significant amount of big data breaches happened because hackers could connect to the enterprise computer systems physically penetrating the office building with the help of social engineering or even dumpster diving and finding confidential documents among the garbage. Many organizations are turning to physical security solutions like ones listed here to ensure the safety of their equipment and data across multiple locations.

Tip 4. It takes on average 200 days for big corporations to detect an intrusion. Early warning systems help to reduce it to several hours. It is crucial to monitor your networks and detect unusual patterns.
Tip 5. Companies should not ask for data they do not really need. For instance, healthcare institutions must introduce a unique patient ID number and do not require the SSN.
Tip 6. Prioritize your defenses. In limited budget conditions, put emphasis on defending the most critical data.
Tip 7. Always encrypt important data.
Tip 8. Provide server access rights to your workers based on their place in a company’s hierarchy.
Tip 9. Conduct penetration tests and risk assessments on regular basis.
Tip 10. Keep up with new security techniques and products. Follow news on recent hacks.
If you are putting any private data online, be ready for the worst-case situation. What is once put online – stays there forever and eventually gets leaked sooner or later. Security challenges multiply as IoT (the Internet of things) and the cloud get more common and new data-stealing strategies appear on the computer crime arena. In many instances, though, our simple suggestions above and a bit of carefulness can save you from the fuss of handling the consequences of a breach.





